Long username? Okta says: no password needed!
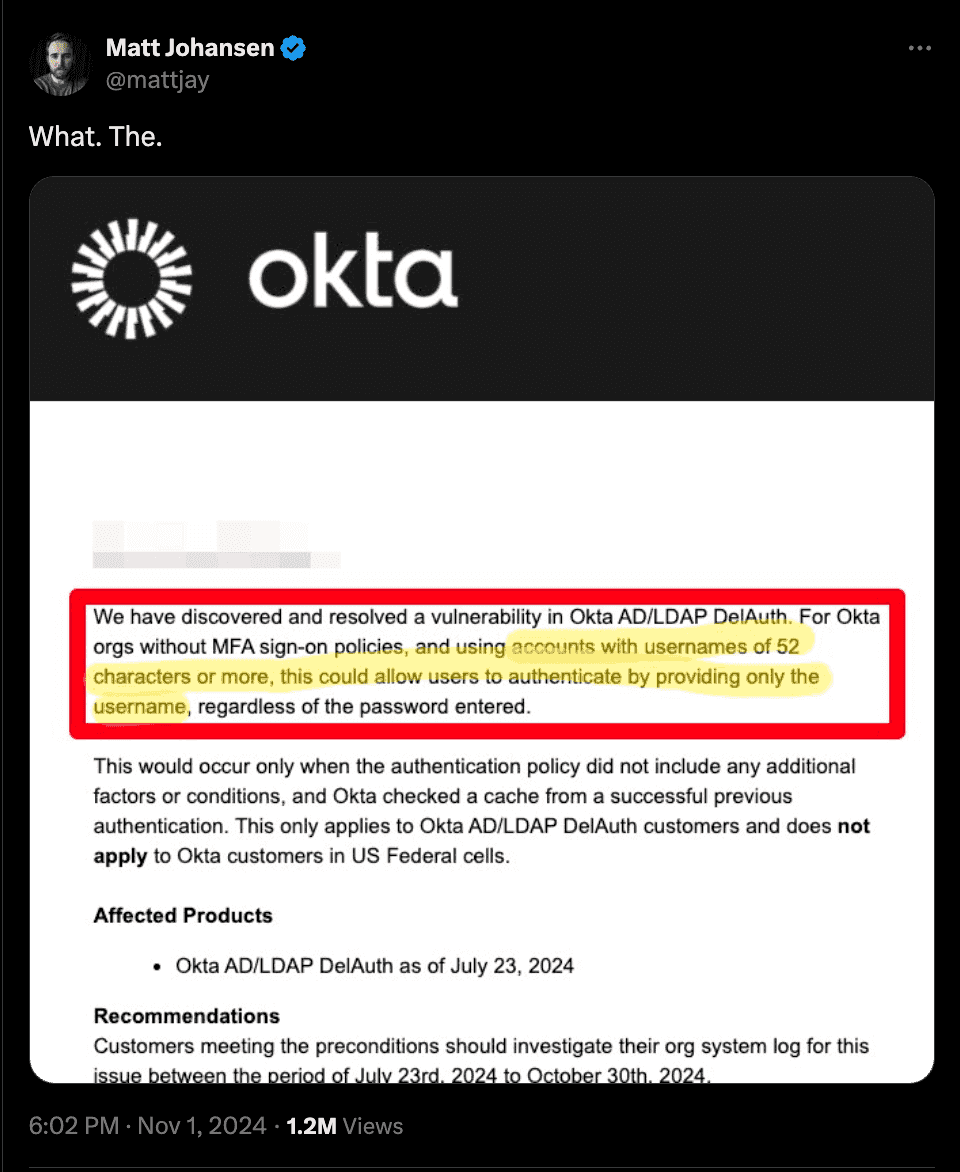
Late last Friday, Okta released a security advisory: accounts with a username of 52 or more characters could authenticate with only the username under some conditions.
From their own description:
"The Bcrypt algorithm was used to generate the cache key where we hash a combined string of userId + username + password."
THIS IS CRAZY!
Bcrypt is a hashing algorithm. The way it is intended to be used is by concatenating a password with a random salt. Concatenating a user ID with a username with a password - this phrase alone should raise the hackles of any security professional - is definitely not a standard usage of Bcrypt.
At best, Bcrypt is a (now not-so-frequently chosen) password hashing algorithm, not a method for generating cache keys by throwing a bunch of user info into one big string. Passwords shouldn't go in cache keys. Public/guessable data like usernames shouldn't go in password hashes. This is more than a weird corner-case vulnerability; this is TERRIBLE security design.
Bcrypt has a maximum input length of 72 bytes. You can probably guess the rest of the issue from here: start with a user ID, then add a username, ...then a password, if there's room left. No room left? Guess we don't need to check if the password matches at all!